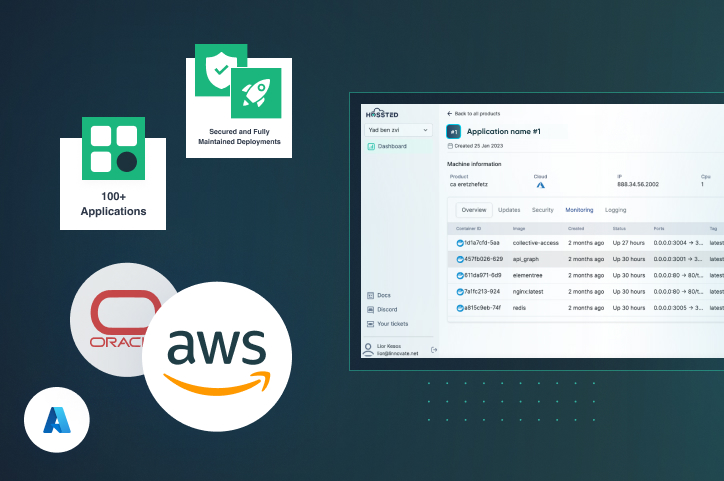
Deployment + Maintenance
Deploy open-source applications instantly on your cloud
- Simple Instant Deployment Instantly deploy in your company’s cloud on.
- Robust Security Continuous security scans to ensure your deployment is safe.
- Control Dashboard Easily manage your open-source applications.
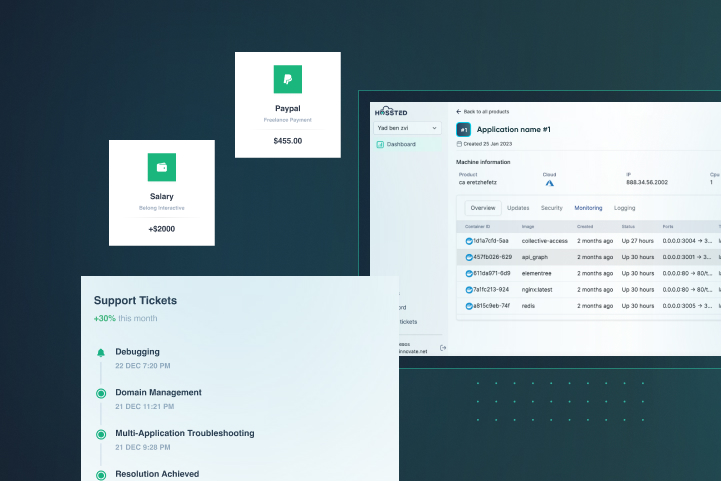
Support
Support all of your open-source applications with one SLA
- 30 Minute Response Time Our support team will reach out to you within 30 minutes of you contacting our team.
- Support Any Time You Need It (24/7) Regardless of your time zone or location, our team of dedicated support professionals can always assist you.
- Quick Resolution Guaranteed On average our team of experts will be able to solve any problem you have ithin 48 hours.
Features
- Data flow management: Design, automate, and manage data flows across systems and applications.
- Visual interface: Create data pipelines with a drag-and-drop interface for easy configuration.
- Built-in processors: Process data in real-time with a library of built-in processors for data transformation, routing, and enrichment.
- Scalability and reliability: Scale data processing pipelines horizontally and ensure reliability with clustering and fault tolerance.

About Apache Nifi
Apache NiFi supports powerful and scalable directed graphs of data routing, transformation, and system mediation logic.
Apache NiFi includes the following capabilities:
- Browser-based user interface
- Seamless experience for design, control, feedback, and monitoring
- Data provenance tracking
- Complete lineage of information from beginning to end
- Extensive configuration
- Loss-tolerant and guaranteed delivery
- Low latency and high throughput
- Dynamic prioritization
- Runtime modification of flow configuration
- Back pressure control
- Extensible design
- Component architecture for custom Processors and Services
- Rapid development and iterative testing
- Secure communication
- HTTPS with configurable authentication strategies
- Multi-tenant authorization and policy management
- Standard protocols for encrypted communication including TLS and SSH